Working Remotely: Risky Business?

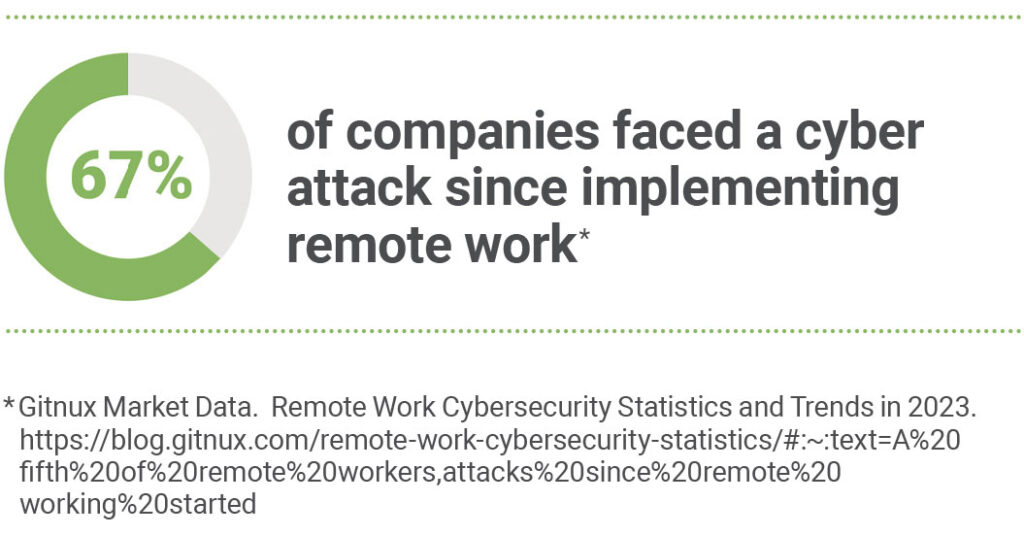
Today’s employment landscape exists largely in a virtual environment with many people working remotely on a full- or part-time basis. While off-site access to the job offers benefits to both an organization and its staff, remote work has widened the gateway for cyber crime as hackers prey on network vulnerabilities.
To lessen the risk of cyber attacks, employers should consider investing in systems and software designed to protect the company’s digital infrastructure. (Learn more about countermeasures and controls by reviewing our GUARD Wire Cyber Security Series at www.guard.com.)
Employees should be made aware that they are part of the organization’s “human firewall,” a key element in combatting cyber threats. All employees should be required to know and adhere to company policies regarding access to the network.
Other tips for remote work are shared here.
Tips for Employees
- Give yourself some space.
If possible, set up your work space in a private area or separate room away from people, noise, and other distractions. - Use only company-issued equipment.
Avoid working from personal computers, tablets, and cell phones. Don’t connect personal equipment, like printers, cameras, or thumb drives, without company approval. - Avoid uploads and downloads.
Don’t install any software on your computer without prior authorization. - Keep it closed and close.
Lock your computer screen when you step away. Never leave equipment unattended in a public setting. - Be private with passwords.
Don’t share passwords with family, roommates, or visitors and avoid entering your credentials when anyone is nearby. - No sharing.
Don’t allow other individuals to use your work-issued computer, especially for internet browsing. - Keep it quiet.
Don’t make announcements on social media that you are working remotely.
Disclaimer: The GUARD Wire is designed to provide general information about various topics of interest and should NOT replace the guidance, advice, or recommendations from licensed insurance or legal professionals, other industry experts, or state and federal authorities.


